The Green Sheet Online Edition
July 25, 2011 • 11:07:02
HIPAA compliance fundamentals for ISOs
It seems every week brings us more headline-grabbing news of the latest data breach. Not only have Payment Card Industry Data Security Standard-related breach incidents escalated, but compromises to public health information have raised concerns among health care professionals. By understanding the complex issues surrounding health care compliance, ISOs can build better relationships in this thriving sector.
In 1996 the Department of Health and Human Services (HHS) published the Health Insurance Portability and Accountability Act (HIPAA). HIPAA presents significant challenges to the more than 1 million merchants involved in health care who are known as "covered entities." By definition, these entities provide care, services or supplies related to the health of an individual and transmit health information in electronic form. HIPAA makes no distinction as to the size of the health care merchant. Smaller organizations must comply with all HIPAA requirements, just as larger health care providers, health insurance companies and health plans do. However, the HHS does give providers the flexibility to design their own privacy procedures.
This article will concentrate on the health care provider segment, which includes doctors, psychologists, dentists, chiropractors, clinics, nursing homes and pharmacies. In some cases, HIPAA can even include fitness centers, spas and masseuse offices that meet the very broad HIPAA definition of a business associate of a covered entity.
HIPAA core requirements
The following describes some HIPAA compliance components that smaller health care providers must perform.
- Each provider must designate a privacy officer. In many cases the office manager is designated as the privacy officer. It is this individual's responsibility to ensure all patient records are kept in a secure place and that only authorized personnel with specific needs have access to records. The privacy officer is required to study the HIPAA Privacy Rule and make sure staff members are informed and in compliance with the rule. Staff members must sign documentation to that effect.
- Each covered entity must perform risk analysis. If the clinic is using a computer to store patient information, the privacy officer must ensure alignment with best industry practices and perform a risk analysis to determine whether there is a possibility the electronically protected health information could be compromised in any way. The files must be backed up, in case of electronic failures, and all information must be properly protected.
- Each covered entity must establish a patient notification policy. No matter how small the provider, the HIPAA Privacy Rule requires that every patient be informed about his or her privacy rights. A written notice must be provided.
- Each covered entity must post a privacy notice. HIPAA requires that each covered entity, including small clinics and medical practices, post its entire privacy notice in the facility.
Health care compliance procedures
If a compromise or breach of health care data should occur, HHS requires specific actions to be taken by the covered entity. HIPAA defines a data breach as follows:
"A breach is, generally, an impermissible use or disclosure under the Privacy Rule that compromises the security or privacy of the protected health information such that the use or disclosure poses a significant risk of financial, reputational, or other harm to the affected individual." Following a breach of unsecured, protected health information, covered entities must provide notification of the breach to affected individuals, the Secretary of HHS, and, in certain circumstances, to the media.
- Individual notice: Covered entities must notify affected individuals following the discovery of a breach of unsecured, protected health information. These individual notifications must be provided without unreasonable delay and in no case later than 60 days following the discovery of a breach.Notice must include a description of the breach, a description of the types of information involved in the breach and the steps affected individuals should take to protect themselves from potential harm. A brief description of actions the covered entity is taking to investigate the breach, mitigate harm and prevent further breaches, as well as contact information for the covered entity are also required.
- Media notice: Covered entities that experience a breach affecting more than 500 residents of a state or jurisdiction are required to provide notice to prominent media outlets, in no case later than 60 days following the discovery of a breach.
- Notice to the Secretary of HHS: In addition to notifying affected individuals and the media (when appropriate), covered entities must notify the Secretary of HHS of breaches of unsecured protected health information. If a breach affects 500 or more individuals, covered entities must notify the secretary without unreasonable delay and in no case later than 60 days following a breach. If, however, a breach affects fewer than 500 individuals, the covered entity may notify the secretary of such breaches on an annual basis.
- Notification by a business associate: If a breach of unsecured, protected health information occurs at or by a business associate, the business associate must notify the covered entity following the discovery of the breach no later than 60 days from the discovery of the breach.
Penalties for compliance violations
HIPAA compliance violations can incur stiff penalties, as follows:
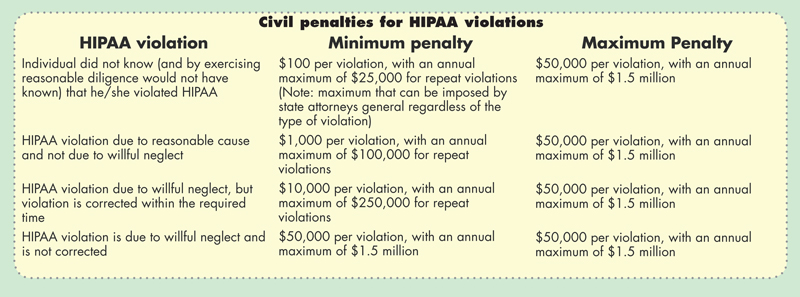
- Civil penalties: The Secretary of HHS has discretion in determining civil penalty amounts. The secretary is prohibited from imposing civil penalties (except in cases of willful neglect) if the violation is corrected within 30 days (this period may be extended). For more detailed information, refer to the "Civil penalties for HIPAA violations" chart in this article.
- Criminal penalties: In June 2005, the U.S. Department of Justice clarified who can be held criminally liable under HIPAA. Covered entities and individuals face fines up to $50,000 and up to one year in prison. Offenses committed under false pretenses allow penalties to be increased to $100,000, with up to five years in prison. Offenses committed with the intent to sell, transfer or use individually identifiable health information for commercial advantage, personal gain or malicious harm, permit fines of $250,000, and up to 10 years in prison.
Here's what you can do to make HIPAA work for you: Educate your merchants; Be a resource for your merchants; Provide merchants with additional resources; Consider selling HIPAA compliant Electronic Medical Record Systems. Given the complexities of HIPAA and the significant and growing level of criminal and civil penalties, it is strongly recommended that HIPAA covered entities align with a company whose principals have the appropriate credentials, including the designation of Certified Information Privacy Professional.

Mark Brady, Consultant at CSRSI and Ross Federgreen, CIPP and founder of CSRSI, can be reached at mbrady@csrsi.com or rfedergreen@csrsi.com, respectively.
Notice to readers: These are archived articles. Contact information, links and other details may be out of date. We regret any inconvenience.





